Quantum computing is no longer a distant laboratory experiment. In 2026, breakthroughs from Google, IBM, and a growing roster of startups have pushed this technology from theoretical curiosity into commercial reality. And with that shift comes a cybersecurity crisis that most businesses are not prepared for.
The encryption protecting your customer data, financial records, and trade secrets today was designed for a world without quantum processors. That world is ending. The question is not whether quantum computers will crack current encryption. The question is whether your business will be ready when they do.
This guide breaks down the quantum threat in plain language. It covers the timeline, the specific risks, the new government standards, and a practical migration roadmap tailored to your business size. No jargon overload. No hype. Just what you need to know and do before 2027.
What Is Quantum Computing (and Why Should You Care About It)?
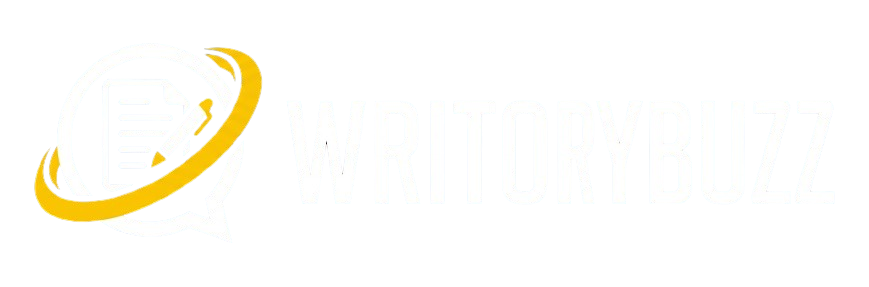
Classical computers process information in bits. Each bit is either a 0 or a 1. Quantum computers use qubits, which can exist as 0, 1, or both simultaneously through a property called superposition.
When qubits interact through entanglement, they can process massive datasets in parallel. Problems that take classical supercomputers thousands of years to solve become solvable in hours or minutes on a sufficiently powerful quantum machine.
For most industries, this means faster drug discovery, better logistics optimization, and improved financial modeling. For cybersecurity, it means something far more urgent.
Why Traditional Encryption Cannot Survive a Quantum Attack
Most internet security relies on RSA and ECC (Elliptic Curve Cryptography). Both depend on mathematical problems that classical computers cannot solve efficiently, specifically factoring large prime numbers and computing discrete logarithms.
A sufficiently powerful quantum computer running Shor’s algorithm can solve both problems exponentially faster than any classical machine. When that happens, RSA-2048 keys, the backbone of online banking, email encryption, and VPN tunnels, become useless.
This is not speculation. It is math. The only variable is timing.
The Quantum Threat Timeline: From Lab to Boardroom
What Is Q-Day?
Q-Day refers to the moment a quantum computer becomes powerful enough to break RSA-2048 or equivalent encryption in a meaningful timeframe. Estimates from leading researchers and intelligence agencies place Q-Day somewhere between 2029 and 2035.
Google issued a warning in February 2026 calling for urgent preparation. The Boston Consulting Group has stated that organizations waiting until 2030 to begin migration will already be too late. The U.S. National Security Agency has set a hard deadline: by January 1, 2027, all new National Security System acquisitions must comply with post-quantum algorithm suites under CNSA 2.0.
Harvest Now, Decrypt Later: The Threat That Is Already Active
You do not need to wait for Q-Day to become a victim.
State-sponsored hackers and sophisticated criminal organizations are already executing “harvest now, decrypt later” (HNDL) attacks. They intercept and store encrypted data today, banking on future quantum capability to decrypt it.
If your organization handles data with a long shelf life (think patient records, classified communications, financial data, or intellectual property), the threat is active right now. Data stolen today could be readable within the decade.
This is the risk that most competitor articles ignore entirely, or mention in a single throwaway sentence. It deserves far more attention because it fundamentally changes the urgency of quantum preparedness.
NIST Post-Quantum Cryptography Standards: What Changed From 2024 to 2026
In August 2024, the U.S. National Institute of Standards and Technology (NIST) finalized its first three post-quantum cryptography standards after an eight-year evaluation process. These are not experimental. They are production-ready and approved for immediate implementation.
The Three Approved Algorithms
| Standard | Algorithm | Purpose | Use Case |
| FIPS 203 | ML-KEM (CRYSTALS-Kyber) | Key Encapsulation | Securing data in transit (TLS, VPNs) |
| FIPS 204 | ML-DSA (CRYSTALS-Dilithium) | Digital Signatures | Code signing, authentication, certificates |
| FIPS 205 | SLH-DSA (SPHINCS+) | Hash-based Signatures | Backup standard, stateless security |
ML-KEM (Module Lattice-based Key Encapsulation Mechanism) replaces the key exchange protocols most vulnerable to quantum attacks. ML-DSA handles digital signatures. SLH-DSA provides a conservative backup option based on hash functions rather than lattice mathematics.
CNSA 2.0 and the NSA 2027 Deadline
The NSA’s Commercial National Security Algorithm Suite 2.0 mandates that all new National Security System procurements use quantum-resistant algorithms by January 2027. Full transition for existing systems must complete by 2030.
While these mandates technically apply to government contractors and defense systems, they create a ripple effect. Any business in the federal supply chain, and any organization that handles sensitive data, should treat these deadlines as guideposts for their own migration planning.
Which Industries Face the Greatest Quantum Risk?
Not every sector faces equal exposure. The quantum threat concentrates where data has long-term value and where encryption is deeply embedded in operations.
| Industry | Primary Risk | HNDL Vulnerability |
| Financial Services | Transaction encryption, digital signatures on contracts | Very High: decades of stored financial data |
| Healthcare | Patient records under HIPAA, research data | Very High: medical records have lifetime relevance |
| Government / Defense | Classified communications, intelligence data | Critical: nation-state adversaries are actively harvesting |
| Legal | Attorney-client privilege, contracts, M&A data | High: legal documents retain sensitivity for decades |
| Energy / Infrastructure | SCADA systems, grid control encryption | Medium: operational data, but long infrastructure lifecycles |
Quantum-Safe Migration: A Practical Roadmap
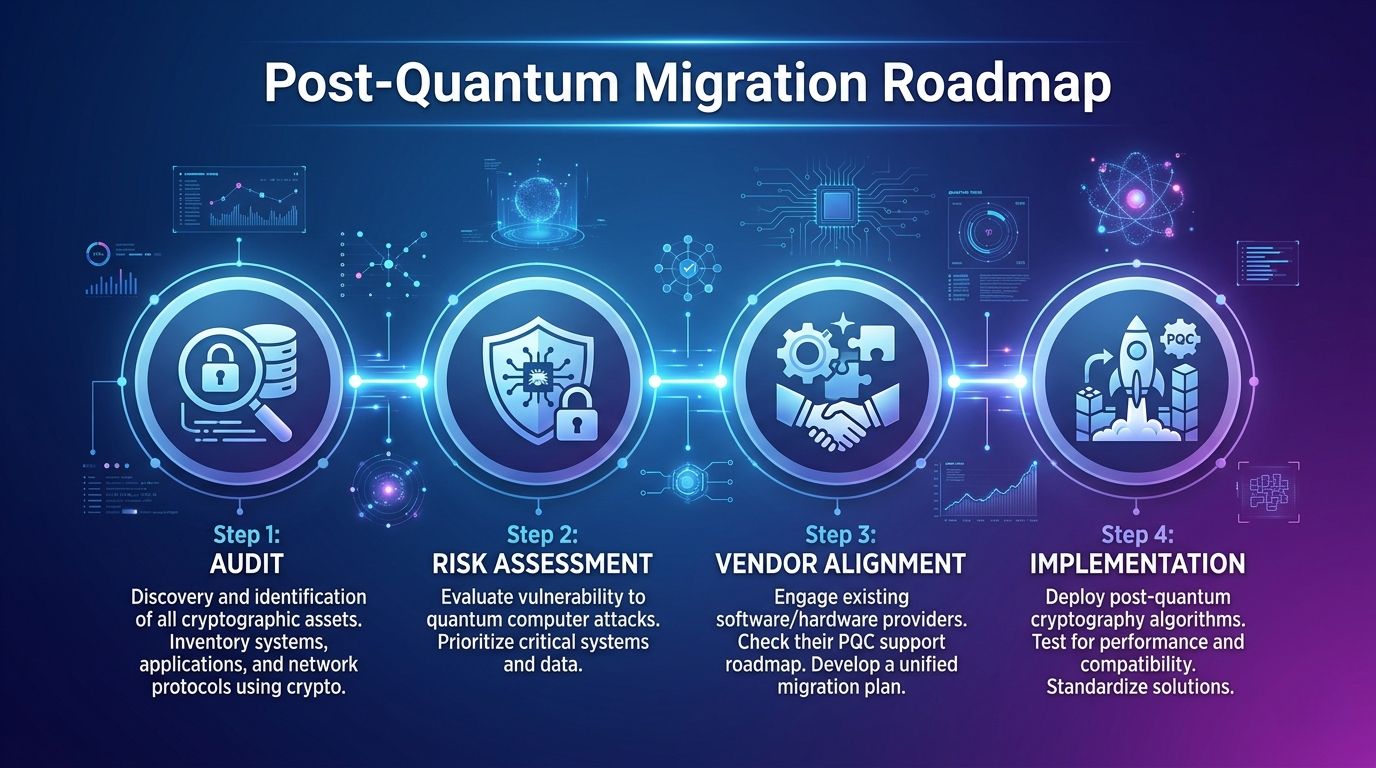
This is where most cybersecurity articles stop. They describe the threat, mention NIST standards, and leave readers without actionable next steps. Here is a concrete migration plan segmented by business size.
Migration Roadmap for Small and Medium Businesses
Phase 1: Cryptographic Inventory (Months 1 to 3)
Catalog every system, application, and third-party service that uses encryption. Document which protocols are in use (RSA, ECC, AES). Most SMBs underestimate how deeply encryption is woven into their operations, from email and cloud storage to payment processing and customer portals.
Phase 2: Risk Assessment (Months 3 to 6)
Score each system based on data sensitivity and lifespan. Patient records and financial data rank highest. Marketing analytics rank lowest. Prioritize systems where a “harvest now, decrypt later” scenario creates real damage.
Phase 3: Vendor Alignment (Months 6 to 12)
Contact your cloud providers, SaaS vendors, and payment processors. Ask about their post-quantum migration timelines. Major providers like Microsoft, Google Cloud, and AWS have published PQC roadmaps. If your vendor has no plan, that is a red flag.
Phase 4: Implementation (Months 12 to 24)
Begin transitioning to hybrid encryption (running quantum-safe and classical algorithms in parallel) for your highest-risk systems. Use NIST-approved libraries and frameworks. Test thoroughly before full deployment.
Migration Roadmap for Enterprise Organizations
Phase 1: Enterprise-Wide Cryptographic Audit (Months 1 to 6)
Deploy automated cryptographic discovery tools across all business units. Map every certificate, key, and protocol. Large enterprises typically find 40% more encryption usage than they expected.
Phase 2: Governance and Policy (Months 3 to 9)
Establish a Quantum Readiness Task Force with representation from IT, security, legal, and compliance. Draft a post-quantum migration policy. Align with CNSA 2.0 timelines if you operate in or serve the government sector.
Phase 3: Pilot Deployment (Months 9 to 18)
Run hybrid encryption pilots on non-critical systems first. Measure performance impact, because post-quantum algorithms generally produce larger key sizes and may affect latency. ML-KEM key sizes are roughly 2 to 3 times larger than equivalent RSA keys.
Phase 4: Full-Scale Migration (Months 18 to 36)
Roll out quantum-safe encryption across all systems, prioritizing external-facing services, data-at-rest encryption, and certificate infrastructure. Budget appropriately. Industry estimates project the global enterprise PQC migration market at over $15 billion by 2030.
Five Expert Tips to Start Your Post-Quantum Journey Today
- Do not wait for Q-Day to act. The harvest now, decrypt later threat means your data is at risk today. Migration takes years, not months. Starting in 2026 puts you ahead of the curve. Starting in 2030 puts you behind it.
- Begin with a cryptographic inventory. You cannot protect what you have not cataloged. Use automated discovery tools if your environment is complex. Manual audits work for smaller organizations.
- Demand PQC roadmaps from your vendors. Your security is only as strong as your weakest vendor. If a critical supplier has no quantum migration plan, escalate that conversation immediately.
- Plan for hybrid encryption as a transition phase. Running classical and quantum-safe algorithms simultaneously is the recommended approach during migration. It maintains backward compatibility while adding quantum resistance.
- Invest in team education. Post-quantum cryptography uses fundamentally different mathematics than RSA or ECC. Your security and engineering teams need training, not just new software.
Common Mistakes Businesses Make When Ignoring Quantum Threats
Assuming Q-Day is too far away to matter. Even conservative estimates place it within 10 years. Migration timelines for large organizations typically run 3 to 5 years. The math does not leave room for procrastination.
Treating PQC as purely an IT problem. Quantum readiness touches legal compliance, vendor management, insurance, and business continuity. It requires cross-functional leadership.
Ignoring harvest now, decrypt later entirely. If your competitors and regulators recognize this threat and you do not, you face both security and reputational risk.
Waiting for “perfect” quantum-safe solutions. NIST standards are finalized and production-ready. Waiting for the next generation of algorithms is a delay tactic, not a strategy.
Underestimating migration costs and timelines. Post-quantum migration is a multi-year, budget-intensive project. Early planning reduces both cost and disruption.
Frequently Asked Questions
What is Q-Day and when will it happen?
Q-Day is the projected date when a quantum computer becomes powerful enough to break RSA-2048 or equivalent encryption. Most expert estimates place Q-Day between 2029 and 2035, though some researchers believe breakthroughs could accelerate the timeline. The uncertainty itself is a reason to prepare now rather than wait.
How can small businesses protect data from quantum computing threats?
Start with a cryptographic inventory to map every encryption protocol your business uses. Then prioritize systems based on data sensitivity. Contact your cloud and SaaS vendors about their PQC plans. For the highest-risk systems, begin migrating to NIST-approved quantum-safe algorithms using hybrid encryption that maintains backward compatibility.
What are the new NIST post-quantum encryption standards?
NIST finalized three standards in August 2024: FIPS 203 (ML-KEM for key encapsulation), FIPS 204 (ML-DSA for digital signatures), and FIPS 205 (SLH-DSA for hash-based signatures). These are built on lattice-based and hash-based mathematics that quantum computers cannot efficiently attack. They are approved for immediate production use.
Your Next Step
Quantum computing will rewrite the rules of cybersecurity. The organizations that act now will transition smoothly. Those that delay will scramble under pressure, with higher costs, greater risk, and less time.
Start with a cryptographic inventory this quarter. Identify your highest-risk systems. Ask your vendors about their quantum migration plans. These three actions take no budget approval and no new software. They take awareness and initiative.
The quantum clock is ticking. The good news? You still have time to get.